Most readers would agree that managing infrastructure can be complex and time-consuming.
Mastering infrastructure as code techniques on AWS promises to simplify infrastructure automation across development environments.
This in-depth guide from the AWS engineering team covers the key concepts and tools - AWS CloudFormation and Terraform - that allow you to treat infrastructure as software for consistent, efficient provisioning and management at scale.
Introduction to Infrastructure as Code on AWS
Infrastructure as Code (IaC) enables software engineers to automate and manage cloud infrastructure through code. This introductory section will provide an overview of IaC concepts and benefits on AWS.
Defining Infrastructure as Code and Its Relevance to AWS
IaC allows engineers to provision and configure infrastructure resources like servers and databases through machine-readable definition files rather than manual processes. This enables consistency, efficiency, and infrastructure automation.
Some key aspects of IaC:
- Describe desired infrastructure state in template files using a domain-specific language like JSON or YAML
- Templates can be version controlled for change tracking
- Infrastructure can be provisioned automatically based on templates
- Promotes consistency and reduces human error from manual work
IaC principles facilitate robust infrastructure management on AWS by enabling engineers to programmatically create, update, and delete cloud resources.
The Advantages of Automating Infrastructure on AWS
Implementing IaC practices on AWS unlocks advantages like:
- Improved efficiency - Engineers can spin up infrastructure faster by automating provisioning and config based on templates
- Consistency - IaC ensures environments are provisioned correctly every time
- Cost optimization - Unused resources can be deprovisioned programmatically to save costs
- Infrastructure automation - Self-healing and auto-scaling capabilities can be implemented programmatically
By enabling robust automation and management of cloud infrastructure, IaC allows software teams to focus less on infra maintenance and more on application development.
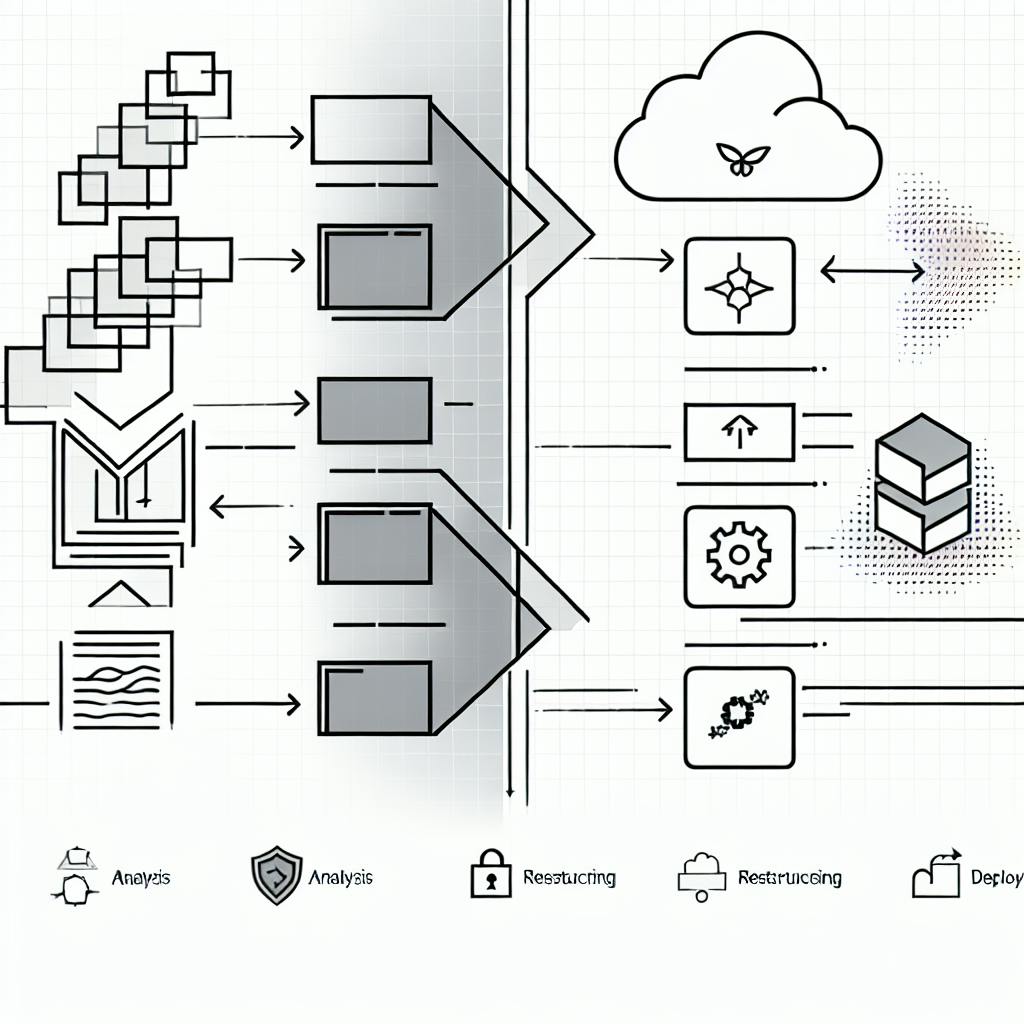
Overview of AWS CloudFormation and Terraform
The main IaC-enabling services on AWS are:
- AWS CloudFormation - AWS native declarative IaC tool for provisioning AWS resources
- Terraform - Flexible imperative IaC tool that can provision resources across AWS, Azure, GCP and other clouds
Both tools allow engineers to define and automate their AWS infrastructure based on code templates versioned in source control. Key differences involve templating formats and architectural paradigms.
Mastering AWS CloudFormation for Infrastructure Automation
AWS CloudFormation allows you to model your infrastructure resources through template files for consistent, automated provisioning. We'll cover the basics of getting started with CloudFormation.
Crafting AWS CloudFormation Templates for Resource Management
CloudFormation uses JSON or YAML templates to model the AWS resources needed for an application. These template files allow you to define the various infrastructure components and configurations required to run your software.
Some key aspects of CloudFormation templates:
- Resources - Specify the AWS resources you want to launch, like EC2 instances, RDS databases, S3 buckets, etc.
- Parameters - Custom inputs that allow flexibility and reuse of templates.
- Mappings - Lookup tables for customizing resource properties based on location.
- Outputs - References to resources once the stack creates successfully.
- Intrinsic Functions - Dynamic variables for transformations within templates.
When building a CloudFormation template, it's best to start simple and add complexity gradually. Define the essential infrastructure first, launch your stack to verify it works, then incrementally increase sophistication.
Follow AWS best practices around security groups, IAM policies, tagging, and other areas to ensure stable and secure applications.
Launching and Managing Your First AWS Stack
Using the AWS Management Console, we'll walk through launching a CloudFormation stack using one of the quickstart templates like a basic VPC or EC2 instance.
To get started:
- Access the CloudFormation section of the AWS Console
- Click "Create Stack"
- Select a template (you can upload your own or choose an AWS sample)
- Input any required parameters
- Configure stack options like tags and permissions
- Click through to launch your stack
Monitor the "Events" tab to track the provisioning status. Once the stack reaches a CREATE_COMPLETE status, the resources defined in the template will be live.
From there, you can modify template parameters to update the stack and change configurations. You can also delete the stack when finished to terminate all associated resources.
Monitoring AWS CloudFormation Stack Resources and Events
The CloudFormation console provides insight into the component resources provisioned for a stack and tracks status events during launches.
The "Resources" tabs lists all infrastructure components deployed by the stack, like EC2 instances, security groups, S3 buckets, etc. You can click through to inspect settings of each individual resource.
The "Events" tab records every step during stack creation and updates. This serves as an audit trail for troubleshooting errors. Any issues around insufficient permissions, unavailable resources, or unsupported parameters will surface in the event log.
Tagging stack resources is highly recommended for tracking origins across deployments. Resource groups can also help organize infrastructure deployed via CloudFormation.
Thorough monitoring through CloudFormation events and resource exploration helps maintain stable stacks and quickly address provisioning failures.
Advanced AWS CloudFormation Techniques for Infrastructure Management
Now that we've covered the basics, we'll explore some of the central concepts and capabilities that unlock the power of infrastructure as code with CloudFormation.
Dynamic Infrastructure Provisioning with CloudFormation Parameters
Parameters allow custom inputs to be passed in at stack launch time for dynamic, flexible template reuse. For example, you can define parameters for resource properties like instance type, VPC ID, and security group ID. This enables a single CloudFormation template to be reused across environments by customizing these parameters.
Some key benefits of using parameters:
- Dynamic infrastructure - No need to hardcode values, parameters can be changed per deployment to create different stack configurations.
- Reusable templates - The same template can be used across dev, test, prod with parameterized differences.
- Flexibility - Stack instances can be customized at launch instead of maintaining separate templates.
When defining parameters, you can specify type constraints, allowed values, default values, descriptions and more for validation and ease of use.
Here is an example parameter definition:
"InstanceTypeParameter": {
"Type": "String",
"Default": "t2.micro",
"AllowedValues": [
"t2.micro",
"t2.small"
],
"Description": "Enter t2 instance type"
}
This allows the InstanceType parameter to be customized at stack launch.
Utilizing CloudFormation Intrinsic Functions for Automated Dependencies
Intrinsic functions like Ref and GetAtt enable templates to programmatically reference resources and data. This eliminates hard-coded values and enables resources to dynamically relate to each other.
For example, the Ref function can reference other resource logical IDs to pass values between resources:
"SecurityGroup": {
"Type": "AWS::EC2::SecurityGroup",
"Properties": {
"VpcId": { "Ref": "VPC" },
"GroupDescription": "Allow HTTP traffic"
}
}
Here the security group is dynamically associated with the VPC resource.
Similarly, GetAtt retrieves resource attributes:
"BucketPolicy": {
"Type": "AWS::S3::BucketPolicy",
"Properties": {
"Bucket": { "Ref": "S3Bucket" },
"PolicyDocument": {
"Id": "MyPolicy",
"Statement": [{
"Action": "s3:*",
"Effect": "Allow",
"Resource": { "Fn::GetAtt": ["S3Bucket", "Arn"] },
}]
}
}
}
This allows the bucket ARN to be dynamically retrieved at runtime for the policy statement.
Intrinsic functions enable advanced automation by removing hard-coded dependencies.
Orchestrating Complex Environments with CloudFormation Resource Dependencies
CloudFormation handles resource management order and dependencies automatically to orchestrate full environment deployments in the correct sequence.
For example, when launching a stack with an Auto Scaling group, CloudFormation will first create the VPC, subnets, security groups, launch configuration, etc. before attempting to create the ASG resource. This ensures all dependency resources are in place first.
You can customize the deployment sequence using resource metadata properties:
"DependsOn": ["GatewayAttachment", "VPC"]
This ensures the resource is deployed after the dependencies are created successfully.
Additional metadata can control update policies, deletion policies, creation policies and more.
With full control over resource dependencies, CloudFormation can deploy intricate architectures predictably and reliably via infrastructure as code.
sbb-itb-6210c22
Reusable Patterns in AWS CloudFormation for Efficient Infrastructure Code
CloudFormation provides powerful abstraction capabilities to reuse infrastructure code through mappings, modules, and stacks.
Strategies for CloudFormation Mappings in Template Reusability
Mappings allow templates to define sets of named values that can be referenced throughout the template code. Some effective strategies for using mappings to improve template reusability include:
-
Define region-specific configuration data like AMI IDs, instance types, etc. in a mapping, allowing the same template to be reused across regions.
-
Store common or shared values like VPC CIDR blocks, subnet configurations, resource tags in a mapping to avoid hard-coding values.
-
Parameterize mapping keys to make mapping lookups dynamic based on user-provided input.
-
Break down large mappings into multiple individual mappings based on concern for easier manageability.
-
Reference mappings from nested stacks to pass values down the stack hierarchy.
Composing Reusable Components with Nested CloudFormation Stacks
Nested stacks enable templates to be broken into reusable, composable code components. Benefits include:
-
Encapsulation - Each nested stack can be developed, updated and managed independently.
-
Separation of Concerns - Infrastructure can be broken down into logical building blocks.
-
Reusability - Common patterns can be defined once and reused multiple times.
-
Abstraction - Hide unnecessary details through abstraction.
-
Modularity - Build large systems by combining smaller modular units.
Best practices for nested stacks:
-
Keep them small and focused on a single concern.
-
Minimize stack inter-dependencies.
-
Use stack outputs to pass data between stacks.
-
Watch out for circular dependencies!
Encapsulating Common Patterns with CloudFormation Modules
CloudFormation module packages encapsulate, distribute and reuse infrastructure definitions. Key highlights:
-
Versioning - module versions allow breaking changes without impacting downstream stacks.
-
Access Control - control module access through AWS Identity and Access Management.
-
Composition - compose complex systems by combining modules.
-
Encapsulation - hide unnecessary template details.
-
Reusability - leverage pre-built, high-quality modules.
Module best practices:
-
Make modules self-contained, configurable and reusable.
-
Avoid hard coding values, leverage mappings and parameters.
-
Document modules clearly outlining functionality, inputs and outputs.
-
Use semantic versioning to manage module versions rigorously.
-
Monitor module usage through CloudTrail to improve quality.
Leveraging Terraform for Multi-Cloud Infrastructure Automation
Now that we've covered CloudFormation, we'll explore infrastructure automation across clouds with HashiCorp Terraform.
Comparative Analysis: Terraform Versus AWS CloudFormation
Terraform is a popular open source tool for automating infrastructure provisioning across public and private clouds. In contrast, AWS CloudFormation is a proprietary service tightly integrated with other AWS services.
Here's a comparison of some key differences between the two tools:
- Cloud Support: Terraform works across AWS, Azure, Google Cloud, OpenStack, etc. CloudFormation only works with AWS infrastructure.
- Language: Terraform uses HCL syntax while CloudFormation uses JSON/YAML.
- State Management: Terraform actively manages state to map real infrastructure. CloudFormation relies on AWS APIs to determine state.
- Abstraction: Terraform manages infrastructure resources directly. CloudFormation works at higher levels using stacks.
Overall, Terraform provides a flexible multi-cloud approach while CloudFormation offers richer native AWS functionality.
Building Modular Infrastructure with Terraform Modules
Terraform modules allow you to create reusable components that can be composed together:
- Encapsulation - Modules bundle one or more infrastructure resources together behind an interface.
- Reusability - Modules can be used multiple times to create distinct copies.
- Abstraction - Modules hide unnecessary details from the user.
For example, you could create a reusable module for a load balanced auto-scaled web application server that encapsulates the details of how it works internally.
Modules are analogous to CloudFormation stacks but are natively supported by Terraform.
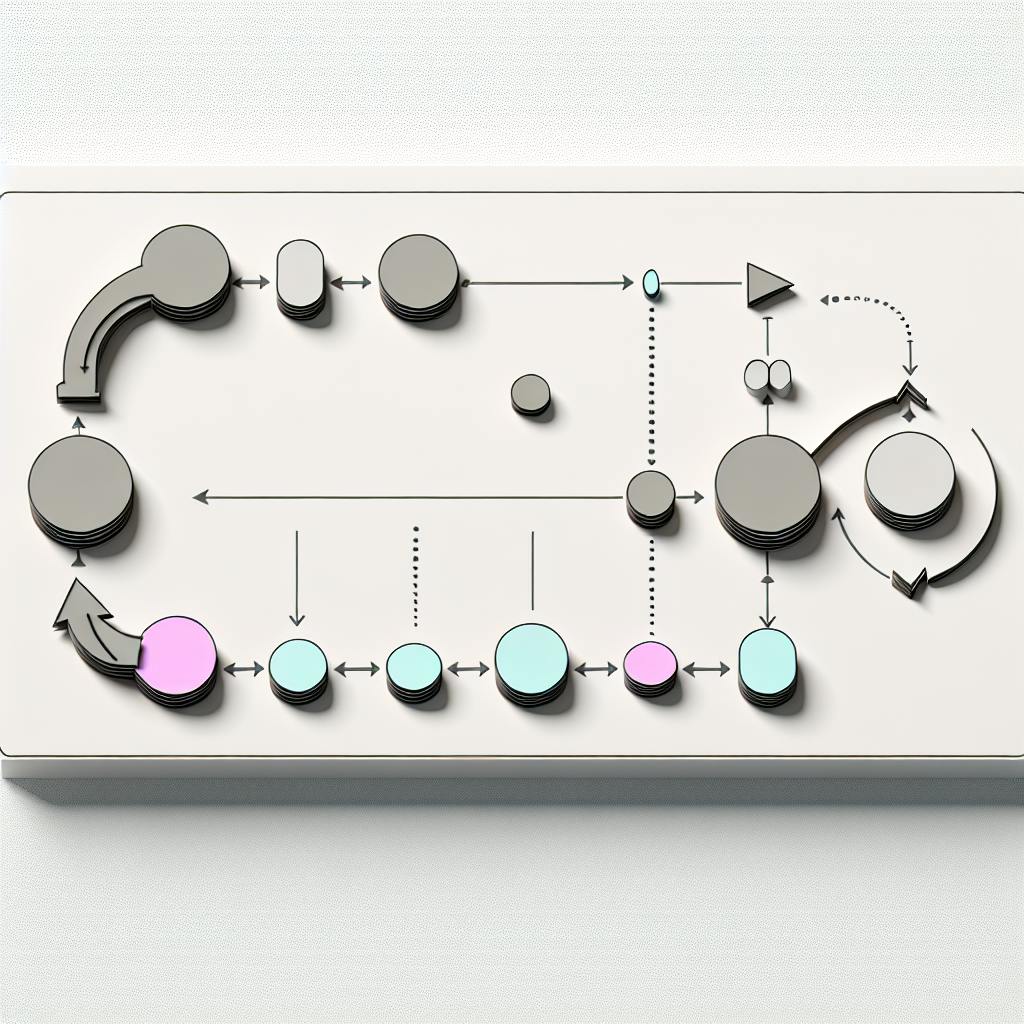
Executing and Managing Changes with Terraform Apply
The terraform apply command handles infrastructure provisioning and changes safely using an atomic plan & execute model:
- Refresh - Refresh state to match real infrastructure
- Plan - Propose changes needed make the infrastructure match the configuration
- Review Plan Changes - Manually verify the proposed changes
- Apply Changes - Provision, update, and destroy infrastructure to match configuration
This workflow allows you to preview infrastructure changes before Terraform executes them. It prevents unwanted changes and provides greater control.
For ongoing management, Terraform stores state which helps it determine what changes are necessary. It offers many capabilities to collaborate on infrastructure changes as a team.
Optimizing Infrastructure Management with Terraform Workflows
Terraform enables powerful version control and collaboration workflows around infrastructure through remote state storage and execution plans.
Implementing Remote State Storage for Terraform Collaboration
Remote backends like S3 or DynamoDB provide a shared source of truth for teams to collaborate on infrastructure. By storing state remotely, multiple engineers can work on the same Terraform configurations. Some benefits include:
- Version Control - State changes are logged over time so you can see who changed what and when.
- Access Control - Use IAM policies to control who can access and modify state.
- Locking - Lock state while Terraform runs to prevent concurrent modifications.
- Backup - Data is stored durably so infrastructure can be easily recovered.
Steps to enable remote state storage:
- Create an S3 bucket and DynamoDB table for storage.
- Configure Terraform backend to use S3/DynamoDB.
- Reference backend and provide access credentials.
Remote state improves Terraform workflows and enables teams to safely collaborate.
Previewing and Validating Changes with Terraform Plans
Terraform plan shows changes that will occur if the configuration is applied. This allows validation before infrastructure changes:
- Review plan output to verify correctness.
- Share and discuss plan to align team expectations.
- Reject unwanted changes by not applying plan.
Benefits of using plans:
- Safety - Avoid mistakes by reviewing first.
- Visibility - Provide transparency to all stakeholders.
- Governance - Enable oversight before changes occur.
Steps to use Terraform plan:
- Make changes to Terraform configuration.
- Run
terraform planto preview changes. - Review plan output and make adjustments if needed.
- Confirm and apply changes with
terraform apply.
Plans enable collaboration by facilitating discussion before applying changes.
Integrating Terraform with CI/CD Pipelines for Automated Deployments
Terraform can integrate with CI/CD pipelines to enable automated infrastructure deployments:
- Testing - Validate infrastructure changes in pull requests.
- Deployment - Apply infrastructure changes post merge to main.
- Destroy - Tear down temporary infrastructure when done.
Example workflow:
- Developer commits Terraform changes to GitHub.
- GitHub Actions runs
terraform planto validate changes. - After approval, pipeline runs
terraform applyto provision real infrastructure. - When feature branch is deleted, infrastructure is destroyed automatically.
Benefits include:
- Speed and safety from test and prod separation.
- Developer productivity freed from manual tasks.
- Infrastructure versioned alongside application code changes.
Automating Terraform through CI/CD improves efficiency and enables scalable infrastructure practices.
Conclusion: Embracing Infrastructure as Code for AWS Cloud Infrastructure
In this post, we've covered the basics of infrastructure as code with AWS CloudFormation and Terraform. To build on these fundamentals, explore implementing these tools in your own projects.
Summarizing Key Takeaways on AWS Services and IaC Tools
Infrastructure as Code (IaC) brings major benefits for managing AWS cloud infrastructure:
-
Consistency - IaC ensures consistent environments by codifying infrastructure in configuration files that can be version controlled and shared across teams.
-
Efficiency - With IaC, engineers can spin up and manage infrastructure faster through automation instead of manual processes. This accelerates development cycles.
-
Cost Savings - By programmatically managing AWS resources, companies reduce waste from orphaned resources and right-size infrastructure to workload demands.
-
Infrastructure Automation - IaC tools like AWS CloudFormation and Terraform provide declarative infrastructure automation capabilities, abstracting manual management.
As covered in this aws engineering blog post, CloudFormation offers native AWS infrastructure as code, while Terraform provides flexibility across cloud providers. Both enable key IaC advantages.
Identifying Next Steps for AWS Cloud Infrastructure Mastery
To build on these IaC foundations, here are some recommended next steps:
-
Work through AWS CloudFormation and Terraform tutorials to gain hands-on experience with syntax, features, and workflows.
-
Explore infrastructure as code best practices like modularity, testing, and organizational collaboration.
-
Implement IaC tools in your own AWS environments to automate management of cloud infrastructure resources like VPCs, instances, and databases.
-
Leverage IaC to enforce organizational standards, achieve consistency, and scale cloud management as your infrastructure grows.
As covered in this aws engineering blog, IaC unlocks game-changing automation for your AWS services. Put these capabilities into practice to streamline cloud operations.